How to fix SSRF Vulnerability?
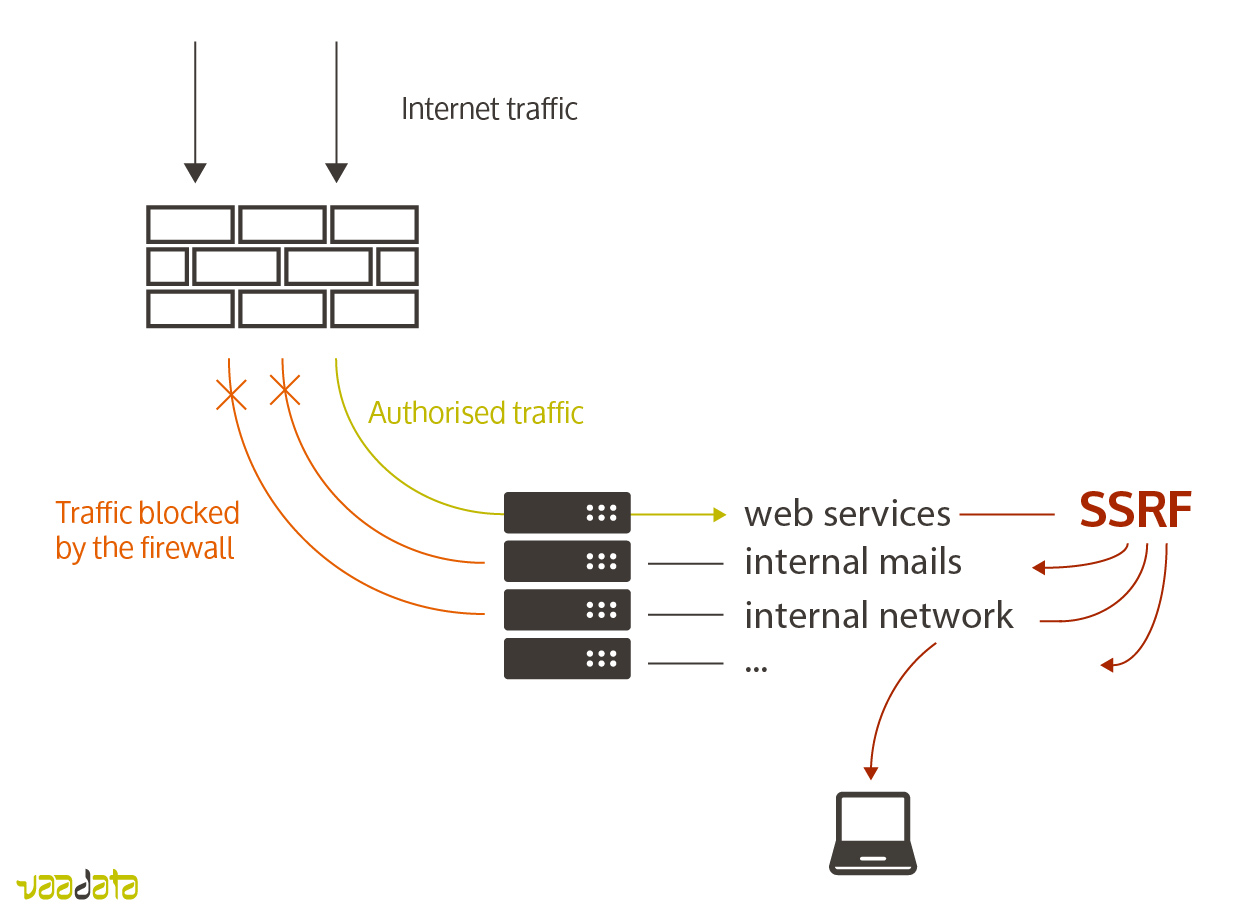
Server-Side Request Forgery (SSRF) is a type of security vulnerability that allows an attacker to send requests from a web server to other internal or external servers, bypassing firewalls and other security measures. This can allow an attacker to access sensitive data, compromise internal systems, or execute malicious code on the server.
To fix SSRF vulnerabilities, you can take the following measures:
- Input validation: Validate user input to ensure that it does not contain URLs or other data that could be used for SSRF attacks. Use a whitelist approach to only allow trusted domains and IPs.
- Restrict access to sensitive resources: Restrict access to sensitive resources such as database servers and internal APIs, and ensure that they are not exposed to external requests.
- Use firewalls: Use firewalls to restrict access to the server and prevent unauthorized requests from being sent.
- Use secure coding practices: Use secure coding practices such as input validation, parameterized queries, and escaping user input to prevent attacks.
- Use secure configurations: Ensure that servers are configured securely, with no unnecessary services or ports exposed to the internet. Also, ensure that default usernames and passwords are changed, and security patches are installed.
- Use security testing tools: Use security testing tools such as penetration testing and vulnerability scanners to identify and fix vulnerabilities.
It is important to note that fixing SSRF vulnerabilities requires a comprehensive approach that includes input validation, access controls, secure coding practices, secure configurations, and regular security testing. By following these measures, you can reduce the risk of SSRF attacks and ensure the security of your web application.